 As with anything else its important to really understand the inner working of the iPhone before attempting to recover any data from it, as two things may happen: the device may be rendered useless or the data on it become contaminated which is just as bad when you are looking for evidence.
As with anything else its important to really understand the inner working of the iPhone before attempting to recover any data from it, as two things may happen: the device may be rendered useless or the data on it become contaminated which is just as bad when you are looking for evidence.
The iPhone runs a custom version of Mac OS X 10.5 (Leopard) with several differences which include:
- an ARM architecture as opposed to the Intel x86 architecture used on desktop machines
- special hardware including an accelerometer, proximity sensor, multi-touch capable screen and several radios including GSM, Wi-Fi and Bluetooth
- a user interface framework built around the iPhone to accommodate the proprietary hardware
- a signed kernel designed to prevent tampering
What can be recovered:
Information stored on the iPhone includes keyboard caches containing usernames, passwords, searches, and some history of what was ever typed on the phone.
Sections of map images from the phone’s Google Maps application, location searches and their coordinates can be found on the phone.
Browser cache and deleted items identifying what websites the user has visited.
Deleted voicemails, email and SMS messages can also be recovered.
A cache of screenshots of the user’s last activities which are kept to improve the experience of opening and closing applications.
Deleted images, address book entries, contacts, calendar events and other personal information can be recovered.
A very detailed call history list beyond what is visibly on the iPhone as well as deleted items from the history.
Disk Layout:
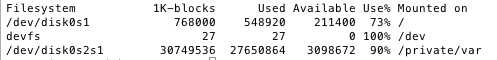
The iPhone uses a solid state NAND flash which is treated as a disk by storing a partition table and a formatted file system. Generally the iPhone will be configured with 2 partitions as shown below.
The first partition is the root which houses the operating system and all the preloaded applications on the iPhone. This partition is read-only and designed to stay like that. The size of the root partition varies depending on the version of the phone (size of the flash).
The remaining space is assigned to the user and is mounted as /private/var as shown above. This allows Apple to upgrade firmware of the devices without in theory touching the user data on the device.
To perform forensics on this type of environment we would need to make the root partition writable to install forensics software in order to maintain the integrity of the data on the user’s data partition.
Communication:
The iPhone can communicate in multiple ways including the serial port, 802.11 Wi-Fi and Bluetooth. AFC or Apple File Connection is a serial protocol used by iTunes to connect to the iPhone and transfer everything from music to software upgrades.
iTunes is not allowed access to the whole iPhone but is rather placed in a jailed environment. People familiar with Linux will understand the term “jailed”, which in general terms mean restricting access and operations to a specific area within the target device.
The hacker community coined the term “jailbreaking” after successfully breaking out of this restricted environment allowing pirated apps to be installed on the phone and unlocking it to be used with other carriers.
The Firmware:
Apple provides firmware updates on a periodic basis which update the operating system, radio baseband and other device firmware. Although these updates have not resulted in loss of user data, it is not recommended that the firmware be upgraded during the forensics process.

![Reblog this post [with Zemanta]](https://img.zemanta.com/reblog_e.png?x-id=ca94d16f-08e5-4cb7-97e1-47a1aebab4e7)
![Reblog this post [with Zemanta]](https://img.zemanta.com/reblog_e.png?x-id=08628cdd-9bdb-4841-ab75-d6bf879ff5f0)


