Without a doubt the whole security professional community have their eyes on the Conficker.C variant which is designed to do something on April 1st.
Without a doubt the whole security professional community have their eyes on the Conficker.C variant which is designed to do something on April 1st.
So what is that something? We’ll find out within 24 hours.
What we do know is that this variant of Conficker has become better at preventing removal and others from taking control of the network of worm infected computers.
The Conficker worm will begin to poll 500 different domain names every day looking for updates to download doubling its current rate.
Interestingly enough one of my most popular posts is on the removal of the Conficker worm from a network environment here and over the last couple of days visitors have exploded exponentially.
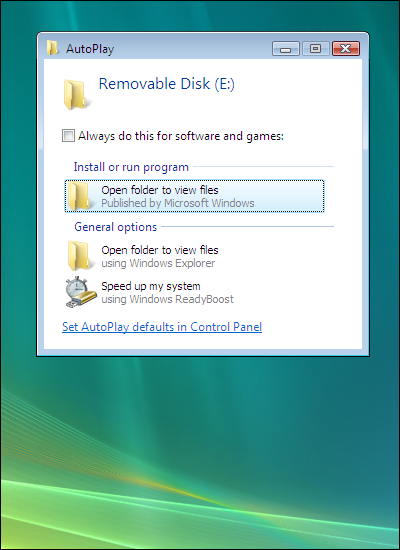
In my two other posts in which I talk about the Microsoft flaw and the Social Engineering components of the worm, I take a rather passive approach to the problem which is based on having contingency plans to prevent, contain and remove the worm from infected computers.
A more pro-active approach would be to look for infected machines without waiting for the symptons to appear by actively scanning the network for computers which have been infected.
Locating computers which have been infected with Conficker using a network scan has kept me up multiple nights, until the guys at Honeynet.org came up with the tool here. Thanks to DShield.org for linking to it in their article on locating Conficker.
[ad]
https://blog.sekiur.com/2009/02/step-by-step-in-dealing-with-conficker/
https://blog.sekiur.com/2008/10/worm-takes-advantage-of-microsoft-flaw/
https://blog.sekiur.com/2009/01/worm-uses-social-engineering/
Related articles by Zemanta
- Your Quick Guide to the Conficker Worm (shankrila.com)
- With global effort, a new type of worm is slowed (infoworld.com)
- My Top Security and Maintenance Tools (idiomag.com)
- New Information Pages on Conficker (blogs.technet.com)
- Windows PC Worm Set to Activate on April 1st (littlegreenfootballs.com)

![Reblog this post [with Zemanta]](https://img.zemanta.com/reblog_e.png?x-id=54f79576-6273-4d40-8fb9-001ff817cc48)