It is my intention next year to attend at least a couple of security conferences if not more.
Below is a list of the most established and ones I found attractive.
CSI

The largest information security conference on the East Coast is also the only security conference expressly assembling experts to challenge the status quo.
CSI thinks that we should forget about tweaking the status quo. We’re already well into a post-perimeter world but without a consensus on the strategic plan moving forward. It’s time to grapple with the issues and technologies that can radically alter the way security works-now, and in the months and years ahead.
Site Link
Defcon

It’s the largest underground hacker convention in the world!
When: July 31 – August 2, 2009
Where: Riviera Hotel & Casino in Las Vegas, Nevada, USA
Cost: $100 (USD) NB. It’s cash only. (free if you’re a full badge Black Hat attendee)
Site Link
Black Hat

The Black Hat Briefings are a series of highly technical information security conferences that bring together thought leaders from all facets of the infosec world – from the corporate and government sectors to academic and even underground researchers. The environment is strictly vendor-neutral and focused on the sharing of practical insights and timely, actionable knowledge. Black Hat remains the best and biggest event of its kind, unique in its ability to define tomorrow’s information security landscape.
When: Various
Where: Las Vegas, Amsterdam, Tokyo, Washington DC
Cost: Varies
Site Link
SecTor

SecTor brings the world’s brightest (and darkest) minds together to identify, discuss, dissect and debate the latest digital threats facing corporations today. Unique to central Canada, SecTor provides an unmatched opportunity for IT Professionals to collaborate with their peers and learn from their mentors. Held at the Metro Toronto Convention Centre in downtown Toronto, SecTor runs two full days. The event features Keynotes from North America’s most respected and trusted experts. Speakers are true security professionals with depth of understanding on topics that matter. SecTor is a must attend event for every IT Professional.
When: October 5-7, 2009
Where: Toronto, Ontario, Canada
Cost: Early Bird: $499, Standard: $749, Full: $999 (CDN)
Site Link
ShmooCon

ShmooCon is an annual East coast hacker convention hell-bent on offering three days of an interesting atmosphere for demonstrating technology exploitation, inventive software & hardware solutions, and open discussions of critical infosec issues. The first day is a single track of speed talks, One Track Mind. The next two days, there are three tracks: Break It!, Build It!, and Bring It On!.
When: February 6-8, 2009
Where: Wardman Park Marriott, Washington DC, USA
Cost: From $100-$300
Site Link
Chaos Communication Congress

The Chaos Communication Congress is an international, five-day open-air event for hackers and associated life-forms. The Camp features two conference tracks with interesting lectures, a workshop-track and over 30 villages providing workshops and gettogethers covering a specific topic.
When: December 27th to 30th, 2008
Where: bcc Berliner Congress Center, Berlin, Germany
Cost: 130 € – 1500 €
Site Link
Toorcon

ToorCon is San Diego’s hacker conference bringing together the top security experts to present their new tricks of the trade and have fun in the sunny and beautiful city of San Diego.
When: September 2009
Where: San Diego, California, USA
Cost: From $120-$200
Site Link
HITB Security Conference

The main aim of our conferences is to enable the dissemination, discussion and sharing of network security information. Presented by respected members of both the mainstream network security arena as well as the underground or black hat community, this years conference promises to deliver a look at several new attack methods that have not been seen or discussed in public before.
When: Various
Where: Dubai, Malaysia
Cost: Varies
Site Link
Phreaknic

PhreakNIC is an annual gathering in Nashville, TN, for hackers, makers, security professionals, and general technology enthusiasts. Hours upon hours of both informative and entertaining presentations are given by volunteers and many areas are set up with the intent of encouraging socialization.
When: October 2009
Where: Nashville, Tennessee, USA
Cost: $25
Site Link
SANS

SANS provides intensive, immersion training designed to help you and your staff master the practical steps necessary for defending systems and networks against the most dangerous threats – the ones being actively exploited. The courses are full of important and immediately useful techniques that you can put to work as soon as you return to your offices. They were developed through a consensus process involving hundreds of administrators, security managers, and information security professionals, and address both security fundamentals and awareness, and the in-depth technical aspects of the most crucial areas of IT security.
When: Various
Where: Various
Cost: Varies
Site Link
Techno Security Conference

TheTrainingCo. is both new and old. As a corporation, it is the culmination of a dream that we have been sharing with people for the past decade. In that sense, it is new. We officially opened our doors in early 1999.
We are old in that the experiences of our senior staff are almost unmatched in their knowledge of the subjects being addressed at our conferences and speaking engagements. Every bit of that hard earned knowledge came as a result of years of highly specialized work and contact with thousands of people. Our two senior members alone bring more than one half of a century of pioneering efforts in the fields of Techno-Security and Cyber-Crime Prevention.
When: May 31 – June 3, 2009
Where: Myrtle Beach, SC, USA
Cost: $895
Site Link
CEIC Conference

CEIC offers lectures and hands-on labs delivered by industry-leading experts, which gives attendees the opportunity to learn the latest techniques and methodologies in computer forensics, eDiscovery, incident response and enterprise investigations.
When: May 17-20, 2009
Where: Loews Royal Pacific Resort, Universal Orlando, USA
Cost: $895
Site Link
IntrusionWorld Conference

The IntrusionWorld Conference & Expo is the forum for business and corporate executives, Industry, government, legal and academic experts that aim to present the state-of-the-art of the practice, emerging technologies in intrusion prevention. Peer-to-peer groups will help us understand the trends and confront the challenges inherent in today’s intrusion prevention technologies, products, systems implementation and risk management. Field practitioners will exchange best practices and lessons learned. Participants will share ideas and expand business and professional contacts during lunch roundtables, workshops, receptions and other activities.
When: May , 2009
Where: Baltimore, MD, USA
Cost: $875
Site Link
The Last Hope
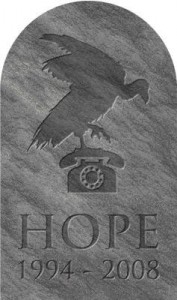
We all knew these days would come. The Last HOPE is the seventh Hackers On Planet Earth conference.
When: July, 2009
Where: Hotel PennSylvania, New York, USA
Cost: $
Site Link
RSA Security Conference

In information security, you’re trained to expect the unexpected. Changes occur in a nanosecond. Stay on top by staying one step ahead — attend RSA® Conference 2008!
Join us for the most comprehensive forum in information security. Come learn about the latest trends and technologies, get access to new best practices, and gain insight into the practical and pragmatic perspectives on the most business critical issues facing you today.
Connect and collaborate. Build your professional network. And mingle with 17,000 of the industry’s best and brightest.
When: April 20-24, 2009
Where: Moscone Center, San Francisco, California, USA
Cost: From $1495 – $3295
Site Link
Info Security Canada

When it comes to your critical information – it’s not a question of if it’s at risk, it’s a question of when. Stay in front of the fast, ever changing information security curve, at Infosecurity Canada 2008, your first and best line of defense.
When: June, 2009
Where: Toronto, Ontario, Canada
Cost: TBD
Site Link
[ad]